This year, the market size value of the healthcare IT market reached $192.2 billion, making more and more people wonder whether it’s time to enter the niche and seize some of that profit. To do that on the US market, you need to not only come up with an innovative app idea but also to make sure that your solution will meet the HIPAA compliance software checklist.
There are laws of this kind in countries all over the world but in this article, we will specifically focus on HIPAA.
HIPAA (Health Insurance Portability and Accountability Act) is a federal law that outlines rules and regulations for health data protection. A HIPAA compliant software is the one that meets the security standards set by this law.
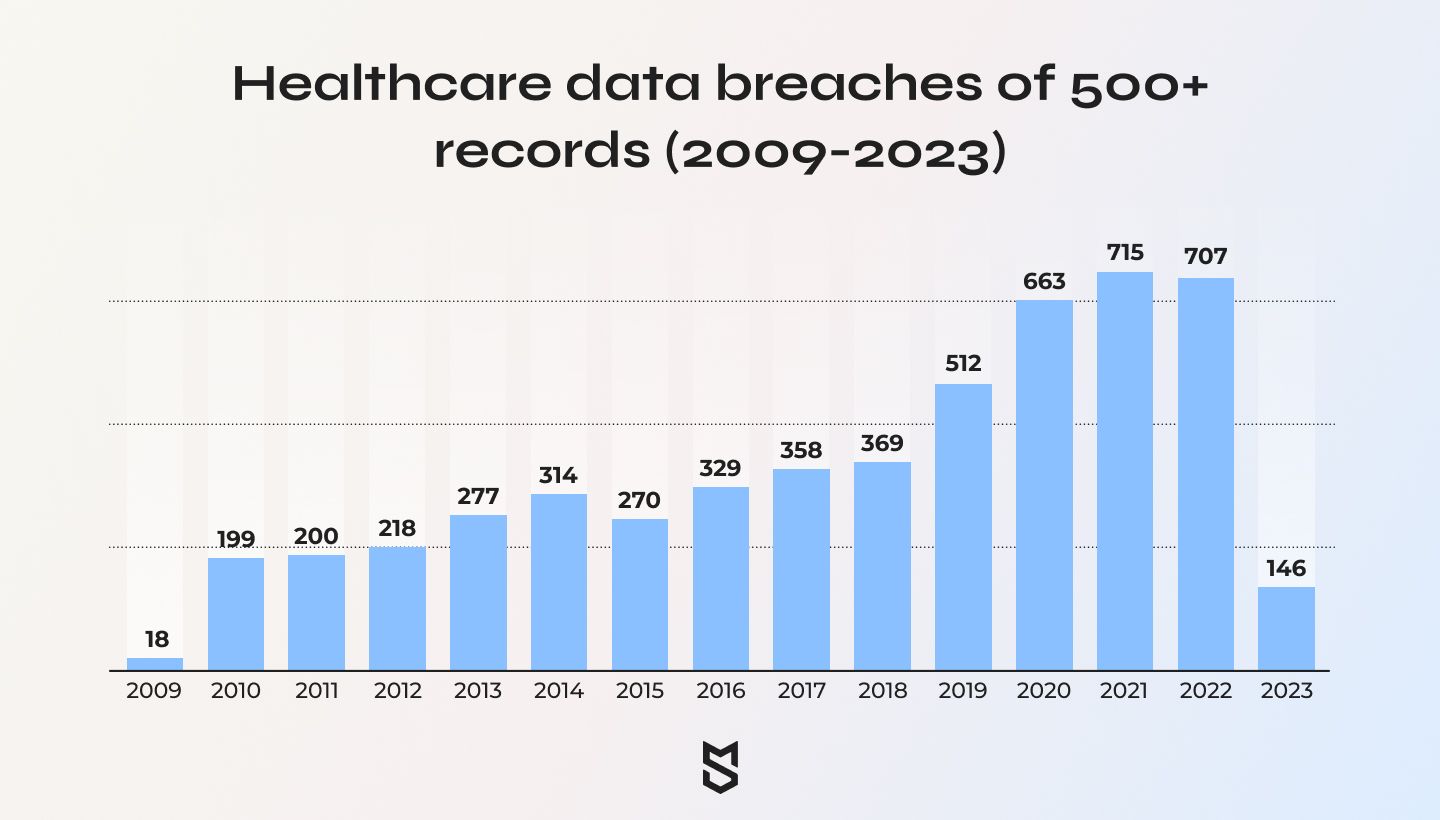
Why is it so important? In 2022, an average of 1.94 healthcare data breaches of 500 or more records were reported each day. This is two times more often than 5 years ago, in 2017. With healthcare data being one of the most sensitive ones, it becomes critical to take serious measures for its protection.
At Mind Studios, we always treat data security seriously. We’ve developed several HIPAA compliant solutions for our clients and will gladly share our knowledge and insights with you. Read further to learn how to make your software HIPAA compliant!
HIPAA Compliance in Healthcare Software Development
The first thing that may come to mind while thinking about a legal act focused on data protection is that it’s very strict to follow. That’s not exactly true. The HIPAA does list the rules clearly as well as states severe penalties for their breaking but also grants you certain liberty in choosing how to apply these rules in the best way.
The following five legal documents must be followed when building HIPAA compliant software.
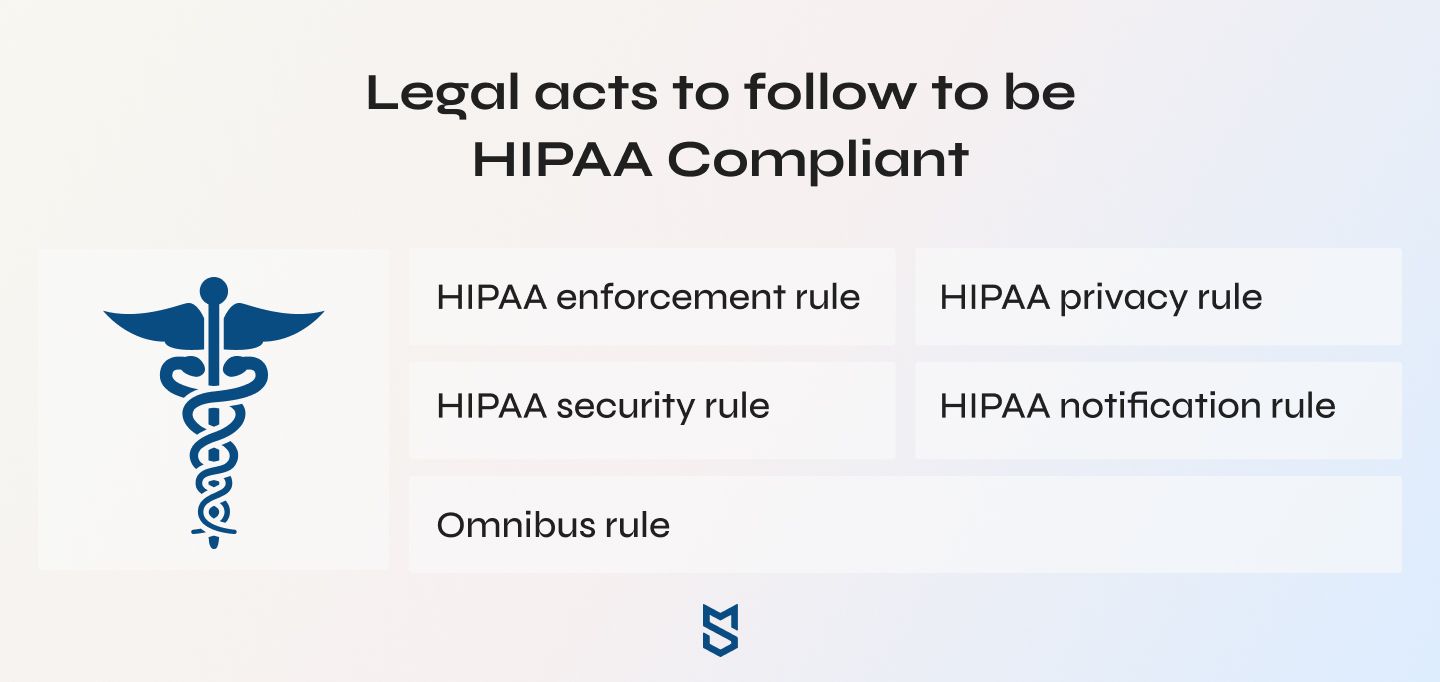
The HIPAA Privacy Rule
The HIPAA Privacy Rule lists standards to protect the medical records and other important PHI (protected health information). This rule enables individuals to control their medical information as they want: view their health records, receive a copy of them, transmit a copy of a record to a third party, and ask to correct the information.
The HIPAA Security Rule
The HIPAA Security Rule sets requirements for the companies that have access to patient data. According to this rule, healthcare organizations have to ensure the integrity, confidentiality, and security of the health information they possess.
The HIPAA Enforcement Rule
While the previous rules set regulations, the HIPAA Enforcement Rule describes the consequences of their violation. This document lists procedures for hearing and civil money penalties. Usually, it takes a data breach or a complaint to start an investigation following this document. However, in some cases investigations can be held without a particular trigger.
The Breach Notification Rule
The Breach Notification Rule gives a detailed definition of a breach and requires software providers and their business associates to immediately notify affected parties when a data leak occurs. Besides informing the patients, users, and official organizations, in certain cases you also need to release a media notice. This regards the breaches that affect more than 500 patients.
The Omnibus Rule
Just like software has its updates, legal acts have their own. The Omnibus Rule was released in 2013 and last reviewed in 2019. This document describes changes made to several other HIPAA rules and is designed to strengthen the data privacy policy. For instance, it introduces new privacy restrictions for using protected health information, updates the breach standards, and extends HIPAA’s liability to business associates.
Steps to Develop a HIPAA-Compliant Healthcare Software
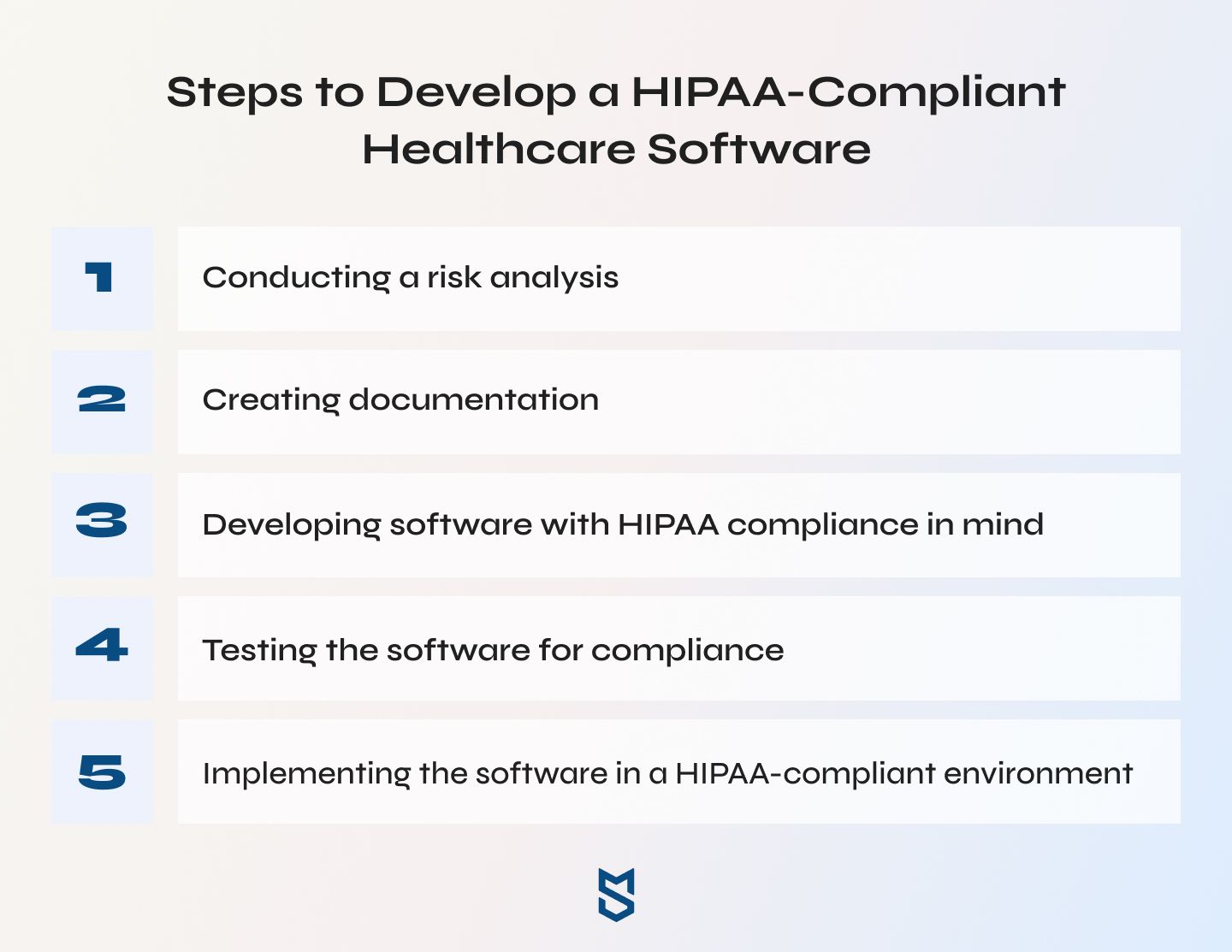
Judging from the number of legal documents created, HIPAA compliant software development might seem like a big challenge compared to more traditional healthcare solutions, such as building medical websites. It is true to a certain extent: after all, compliance depends not only on how you meet technical requirements but also on administrative and communication aspects, which we’ll address later. Following these steps can help you implement the HIPAA requirements more efficiently and easily.
1. Conducting a risk analysis
The first step of HIPAA compliance application development is to evaluate your product, conducting a risk assessment of its policies and IT infrastructure. At this stage, you need to understand your current level of compliance as well as identify what has to be done to meet the HIPAA criteria.
Here are the things that deserve special attention:
- The PHI that you collect from users, store, and share with other organizations or individuals
- Your existing data management policies and procedures
- Data security incident analysis (if you had such incidents before)
- Security mechanisms used for data protection, potential weaknesses in the hospital management systems (HMS) and electronic health records (EHR)
- The impact of possible data breaches
It is worth noting that such a risk analysis should be conducted not only at the beginning of the development process. You should also run it periodically when your product is already fully functioning to spot potential security weaknesses and prevent data breaches.
2. Creating documentation
First and foremost, your software needs to have well-structured documentation. Second, this documentation should be both instantly accessible and stored in a secure repository.
Third, the documentation should include internal policies for emergency situations, such as data breaches or attempts. Because while your software might totally fit the HIPAA Privacy Rule checklist, in the end data a lot will still depend on the human factor and actions taken when an emergency happens. Having precise instructions for such incidents and updating them as technologies progress will help your employees protect sensitive data if anything happens.
3. Developing software with HIPAA compliance in mind
To meet the HIPAA compliance checklist, your software must focus on the following things:
- Secure data storage. This is where you store all the PHI and access them when necessary. Such a server needs to have a signed Business Associate Agreement (BAA) to meet the HIPAA requirements. The data should also be encrypted for advanced protection in case of database hacks.
- Backup and emergency options. They should be designed to help you protect and restore data in case of system failures, power outages, and other malfunctions. All the backup data should also be encrypted.
- Automatic logout. Leaving an account logged in after the user has retrieved the necessary data can lead to someone else accessing the patient records from the same device. Automatic system logout can prevent that — and a potential data breach — from happening.
- Integrity. HIPAA compliant software shouldn’t be accessed and altered by authorized users. There are two common ways to prevent such users from entering your system: you can either use public-key cryptography (SSH, PGP, and SSL) for data encryption or implement blockchain solutions enabling distributed and decentralized data management.
- Data disposal. The PHI that is no longer needed can and should be immediately and permanently deleted. The HIPAA requires providers to destroy the patient data that hadn’t been used for six years or more. The same goes for the data that providers no longer need. There are penalties for storing unnecessary data, so be sure to regularly review health information and delete it.
4. Testing the software for compliance
Any software has to be thoroughly tested before it sees the market, and HIPAA compliant one is definitely no exception. Furthermore, it requires a specific testing approach.
HIPAA compliance software vendors test the software for the following safeguards:
- Access control. Testers check whether all users have a unique name and/or user ID, whether it’s possible to access PHI in case of emergency, and whether the system terminates the session automatically after a certain inactivity period.
- Authentication. Testers ensure that a HIPAA compliant platform grants access only to authorized users and run negative tests (like entering an invalid ID) to confirm that unauthorized users won’t be able to log in.
- Audit control. Testers verify if all the activity is stored in the activity logs, specifically focusing on all the actions regarding PHI access and on user roles that try to access it.
- Integrity. Testers make sure if a platform has all the necessary controls to spot and prevent human errors (such as accidental data changes), enable accurate data backups, and prevent unauthorized PHI altering and deletion.
- Transmission security. Testers confirm that all the data sent via the platform is encrypted and decrypted correctly, without experiencing any modifications in the transmission process.
5. Implementing the software in a HIPAA-compliant environment
Designing a solution that complies with all HIPAA regulations is just part of the process. Another, no less critical part, is to ensure that those who work with that solution understand the importance of PHI and know how to handle them.
How to become HIPAA compliant both in terms of software and the environment? Teach the employees all they need to know about general and HIPAA-related data protection.
This includes:
- learning what data HIPAA covers
- understanding why PHI should be protected
- understanding how exactly data is protected and taking basic security measures (setting up secure passwords, using two-factor or multi-factor authentication for HIPAA-compliant platforms)
- learning about the most common types of cyberattacks (phishing, malware, stolen passwords, etc.) and conducting stress tests to learn how to withstand them
Best Practices for Maintaining HIPAA Compliance

Congratulations! If you followed the HIPAA compliance software checklist listed above, your app is probably good to go. However, the responsibility to protect sensitive data doesn’t end here. The next step of the process is to maintain HIPAA compliance.
Mind Studios can suggest the following best practices that can help you with that:
Managing data
We’ve already addressed the HIPAA requirements regarding old and unnecessary data: it should be deleted permanently. This approach is generally a good one when you have a big chunk of sensitive data stored in your systems.
Here’s what should be regularly reviewed and deleted both from your servers and from portable storage devices:
- PHI data logs
- Duplicated PHI records
- Old backups
- Medical records of previous patients
To make everything easier, you can use special programs to scan for unused data. Just make sure they are trustworthy and secure!
Encrypting data
Data encryption reduces the risks of possible breaches and leaks caused by the human factor. After all, the security of PHI depends not only on measures taken during app development but also on the ways the data is shared.
Users can send unencrypted data via public emails and unprotected cloud services. They can also store such data on personal devices that can be lost or compromised. While you cannot control every human action, you can encrypt the data to prevent massive data breaches.
Implementing access control
Properly implemented access control ensures that PHI will be accessed and used only by people authorized to do so. This is especially crucial for projects that include frequent data sharing between different users.
Here are the most common (and efficient ways) to establish access control:
- unique identifier, also known as UID (one login per user)
- emergency data access protocol
- two-factor or multi-factor authentication
- automatic system logouts
- data encryption
- access monitoring
Improving backup
Critical data can become inaccessible due to various factors, such as:
- server crashes
- ransomware
- data corruption
- and even natural disasters
While things like fires and hurricanes are definitely things you cannot prevent, in any of these cases it’s up to you to ensure that all the important information will be saved and can be used despite the emergency.
To achieve that, you need to develop reliable backup processes as well as come up with a disaster recovery strategy. You can do it yourself: find a secure facility for data backup storage and regularly review its systems to spot and prevent possible failures, conduct daily backups of the most crucial data, and develop detailed backup policies. Or you can also entrust the backups to a trustworthy service provider.
Cost of developing a HIPAA compliant software
The final cost of any healthcare app development, including HIPAA compliant one, depends on several factors:
- project’s complexity
- set of features
- number of supported platforms
- delivery speed and terms
- tech stack
- team size
Basically, the more complex an app is, the more expensive it will be. The average time to build a HIPAA compliant solution is about four months and the average price of such a solution is about $80,000. This covers building an app from scratch, vetting it, and obtaining all the required certifications.
Mind Studios experience
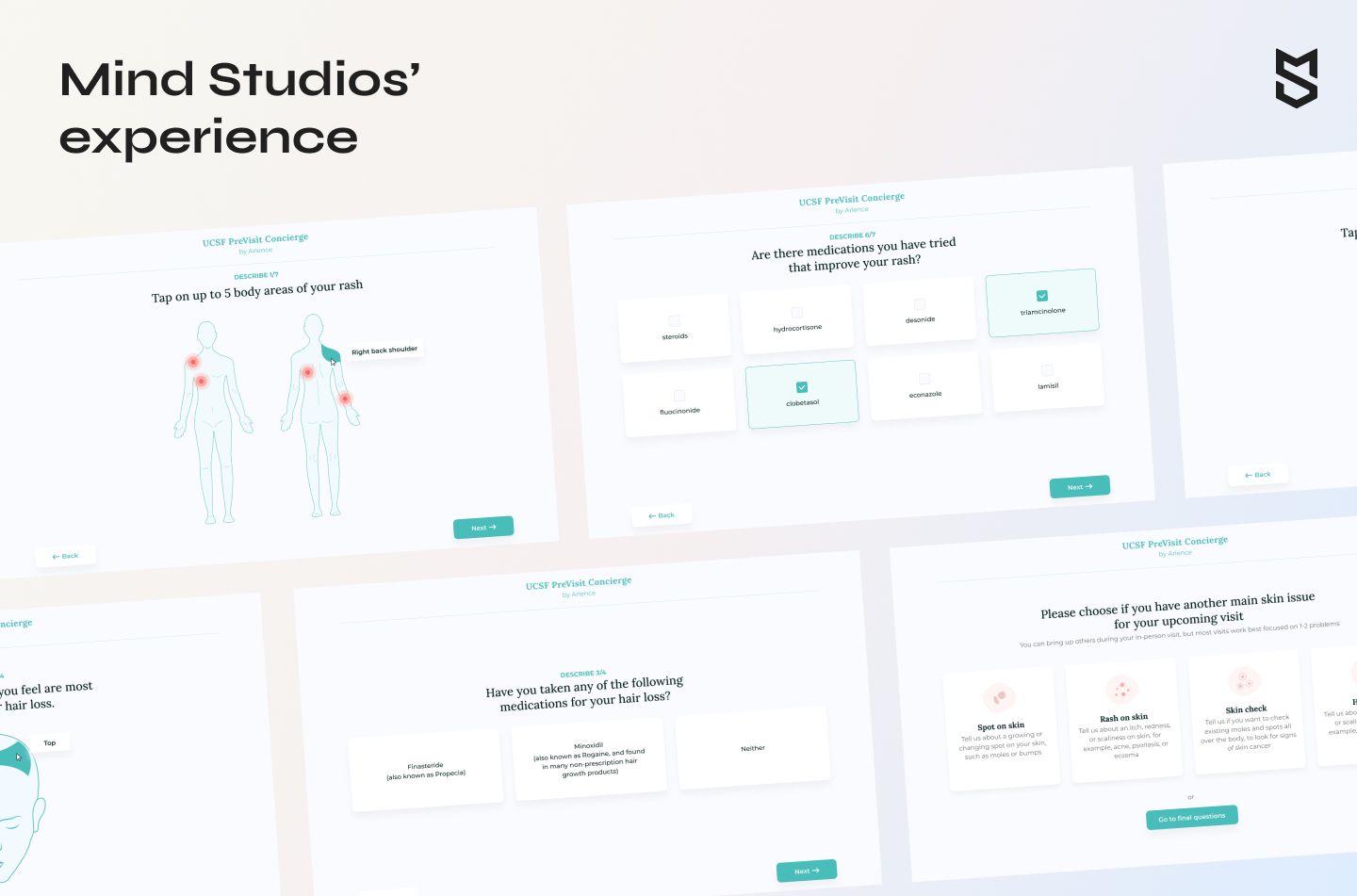
One of our most memorable HIPAA software development cases is a dermatological telemedicine solution designed to optimize both the doctor’s and the patient’s time. A patient registers on the website, sets an appointment with the doctor, and receives an email link to a special online form that they have to fill in.
The form contains the most common questions about the patient’s health and complaints, allows them to add photos of their skin, and provides any additional information that can be useful to the doctor. The doctor, in turn, is able to review this data before the appointment and can already have some suggestions and solutions by the time they contact the patient.
However, a user becomes a patient right after they set up an account, and the data they provide is considered PHI. Therefore, such data requires HIPAA protection and cannot be sent even via email.
Mind Studios came up with the following solution. Instead of offering users the form, we started redirecting them to a protected page. They had to enter their credentials there to access the chat with a doctor. This way, all the conversations were held in the secured space to prevent potential data leakage.
Now when we build HIPAA compliant solutions, we use Epic — a platform used to store private medical records. The platform cooperates with medical institutions, allowing doctors to log in using their credentials. It is widely used, HIPAA compliant, and allows us to rest assured, knowing that all the sensitive data is stored in one of the safest data hostings.
Conclusion
Health Insurance Portability and Accountability Act is a law that regulates the usage of personal health data. It consists of five legal documents, all of which must be followed to build a secure healthcare app.
Data security, encryption, storage, backup, and access control are among the main things one should keep in mind while building a HIPAA compliant app. Even so, complying with HIPAA for software developers might be difficult if they haven’t dealt with this type of project before. There are a lot of things specific to the niche to keep in mind.
That’s why if your goal is to build an HIPAA compliant platform, it’s better to turn to those already familiar with the law’s restrictions and protocols. Mind Studios has successfully delivered several such platforms and knows exactly what to focus on to make your healthcare app truly secure and meet all the HIPAA requirements. Contact us to learn more!