In this article, we offer a guide on how to secure a website from being hacked and used for illegal activities.
Online safety is a huge red flag in the infinite blue sky of the internet. And while the words “online safety” may first bring to mind online harassment and protections for users, the damage a lack of website security can have on a business is also significant. Website owners who cut spending on security pay with their reputations and, consequently, suffer financial losses. Therefore, many of them, after some time, still come to the question of how to protect your website from hackers.
Contents:
- Why every website owner needs to invest in security
- What vulnerabilities are we talking about?
- Injection flaws
- Sensitive data exposure
- Cross-site scripting (XSS) attacks
- Broken authentication
- Security misconfiguration
- Broken access control
- Insecure deserialization
- Insufficient logging and monitoring
- XML external entities (XXE)
- Using components with known vulnerabilities
- How to create a secure website
- How much does it cost to secure a website?
Why EVERY website owner needs to invest in security

Some website owners have thoughts like these: There’s nothing to steal on my website. I don’t keep any user data or payment details. I don’t need expensive top-of-the-shelf security of a website from hackers.
However, that’s just plain naïve. There are a number of reasons why your website might be hacked even if it doesn’t host any personal or financial data. Here’s a list of uses hackers might have for just about any unprotected server:
- To demand a ransom. Even if you don’t keep any user data on your servers, hackers can take them over and demand money from you to get them back.
- To use as an SMTP (simple mail transfer protocol) relay. SMTP is a protocol used to deliver emails in bulk — for example, newsletters. Hackers can use your servers to send spam or ransomware.
- To mine Bitcoins.
- To use in DDoS attacks as part of a botnet.
- To change or delete the data on your website. Reasons for wanting to do so may vary.
And that’s just scratching the surface. Besides threats posed by third parties (hackers and other criminals), there are also threats posed by possible mistakes on the part of employees managing your website, for example. In fact, internal security is as important as external, if not more.
So how can I secure my website from hackers? you ask.
Well, you must account for and deal with a number of vulnerabilities.
What security vulnerabilities are we talking about?
One of the most reputable entities in the industry that concerns themselves with cybersecurity is the Open Web Application Security Project, OWASP for short. The OWASP foundation monitors for and regularly updates their list of widespread web security issues. The following are common security issues on their list (in no particular order) as of the day of writing this article and some tips for how to reduce the danger to your website.
Injection flaws

Injection flaws concern databases and are caused by poor input validation. When your system accepts user input but fails to properly filter that input, it makes the system vulnerable — hackers can exploit this to inject their code into your system (hence the name). This injected code can result in your website performing commands you didn’t intend it to, making it display sensitive data or even give up control of the website to the hacker.
The most popular type of injection vulnerability involves SQL databases, but injection vulnerabilites aren’t really limited to them. XPath queries, LDAP statements, and XML scripts can also be vulnerable to injection.
How to make a website secure from injection flaws? Two of the best practices include using SQL query sanitization and parameterized queries. There are APIs that allow you to do that.
If you don’t want to implement these things by hand, you can use an ORM (object-relational mapping) tool for your preferred programming language. We use ActiveRecord because it’s tightly linked with the Rails ecosystem.
None of the options above are completely fool-proof, but it’s as close as it gets to solid protection these days.
Sensitive data exposure

Sensitive data is any data that can be used to exploit a person in one way or another:
- Name
- Social security number
- Driver’s license number
- Credit card information
- Usernames and passwords
- Date of birth
- Health information
- Maiden name
- Parents’ names
It can even include any information that’s an answer to a security question, say for your bank account. Who would have thought that your first pet’s name could be considered sensitive data, right?
Securing websites from sensitive data exposure is hard, since this exposure is difficult to predict and detect. But there are preventive measures you can take for website protection from hackers. Sensitive data, if stored on a website, must never be stored as plain text; it must be encrypted with the latest technology and transmitted only via secure channels.
If your website facilitates any transactions or generally deals with sensitive data, it needs to use SSL encryption. This is the latest and best encryption technology available. SSL encryption helps you safely transfer data between a browser and a server or between servers. Furthermore, many users will be looking for HTTPS in your website’s address to see whether it’s secure. That header is what you get when you obtain an SSL certificate.
It’s also generally recommended to store data in the cloud. However, don’t assume that simply storing it in the cloud will automatically make the data safe. All protective measures must be implemented nonetheless, and you must regularly monitor and update the security.
Cross-site scripting (XSS) attacks
XSS vulnerabilities are, in a way, similar to injection flaws, as they allow hackers to affect your website pages by injecting non-native code. In the case of XSS, we’re talking about JavaScript injection. JavaScript injected by a hacker can change page content, insert links to malicious websites, and send originally concealed data back to the hacker, resulting in sensitive data exposure.
Ruby on Rails and React have built-in XSS protection. Another option for anti-XSS and anti-injection measures would be using the Content-Security-Policy HTTP response header.
Broken authentication
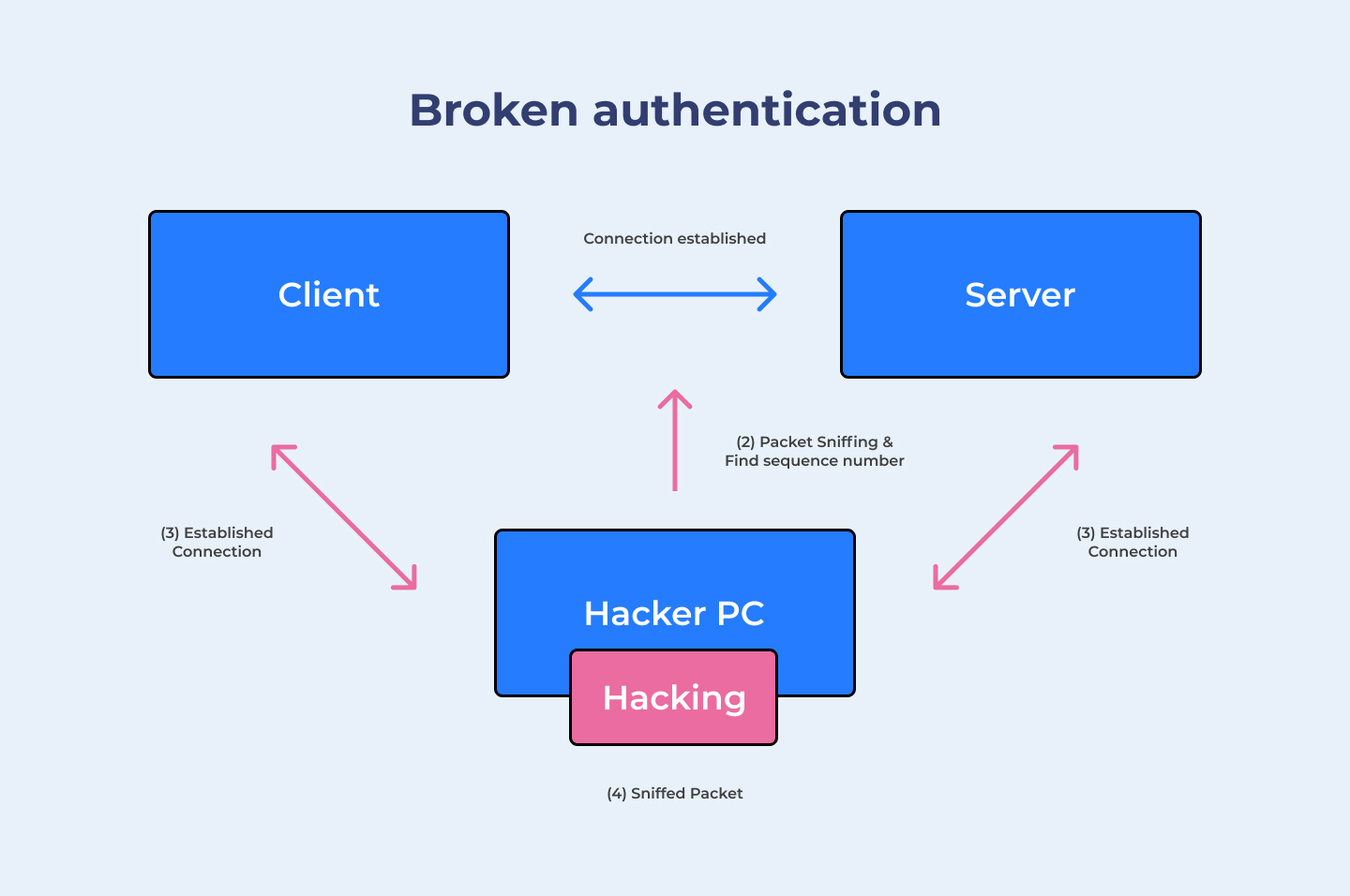
Originally called “Broken authentication and session management,” this flaw deals with vulnerabilities during user authentication and session management, as evident from the name. This includes the exposure of login credentials and a number of issues with session IDs:
- Weak session IDs
- Session IDs showing in URLs
- Session IDs that don’t change between log-ins
- Transmitting session IDs via unsecured connections
Session IDs are directly connected to a user’s identity, the same as credentials, and hence intercepting them can lead to hijacking of a user’s account. This leads to all kinds of damage for your users, from financial and reputational to health-related.
To make your website safe from authentication attacks, require multi-factor authentication: for example, require a constant password and a one-time password delivered to the user’s mobile device.
Google employs an option for two-factor authentication: to open your Google account in a web browser, you need to first enter your password. If it’s correct, you also need to open the Google app on your phone and choose the number shown in the web browser.
More obvious website protection methods for broken authentication include:
- enforcing password complexity — “Your password must be at least 8 characters long and include at least one number, one upper-case letter, and one lower-case letter.”
- limiting login attempts before which the account is suspended (for a specific time or till the user contacts the site admins) and alerting the admins
Security misconfiguration
Security misconfiguration is a wide topic, as this can happen at any stage and with any part of your website: a database, a network, a server, a framework, storage, or just about anything else. This is important if you want to know how to protect a website from hackers. Configuration weaknesses can be exploited to gain access to system functionality. Depending on where the vulnerability is, such access can be partial or complete. Examples of misconfiguration:
- You haven’t disabled default accounts/passwords.
- There are unnecessary and unused features.
- Access permissions to the cloud aren’t securely configured.
- Your error messages display sensitive information like usernames, passwords, or email addresses.
The first thing to do to avoid misconfiguration is to remove all that’s unused — features, samples, frameworks, etc. The next step is to ensure the same configuration for all environments and check its performance regularly. A well-thought-out architecture is a must.
Broken access control
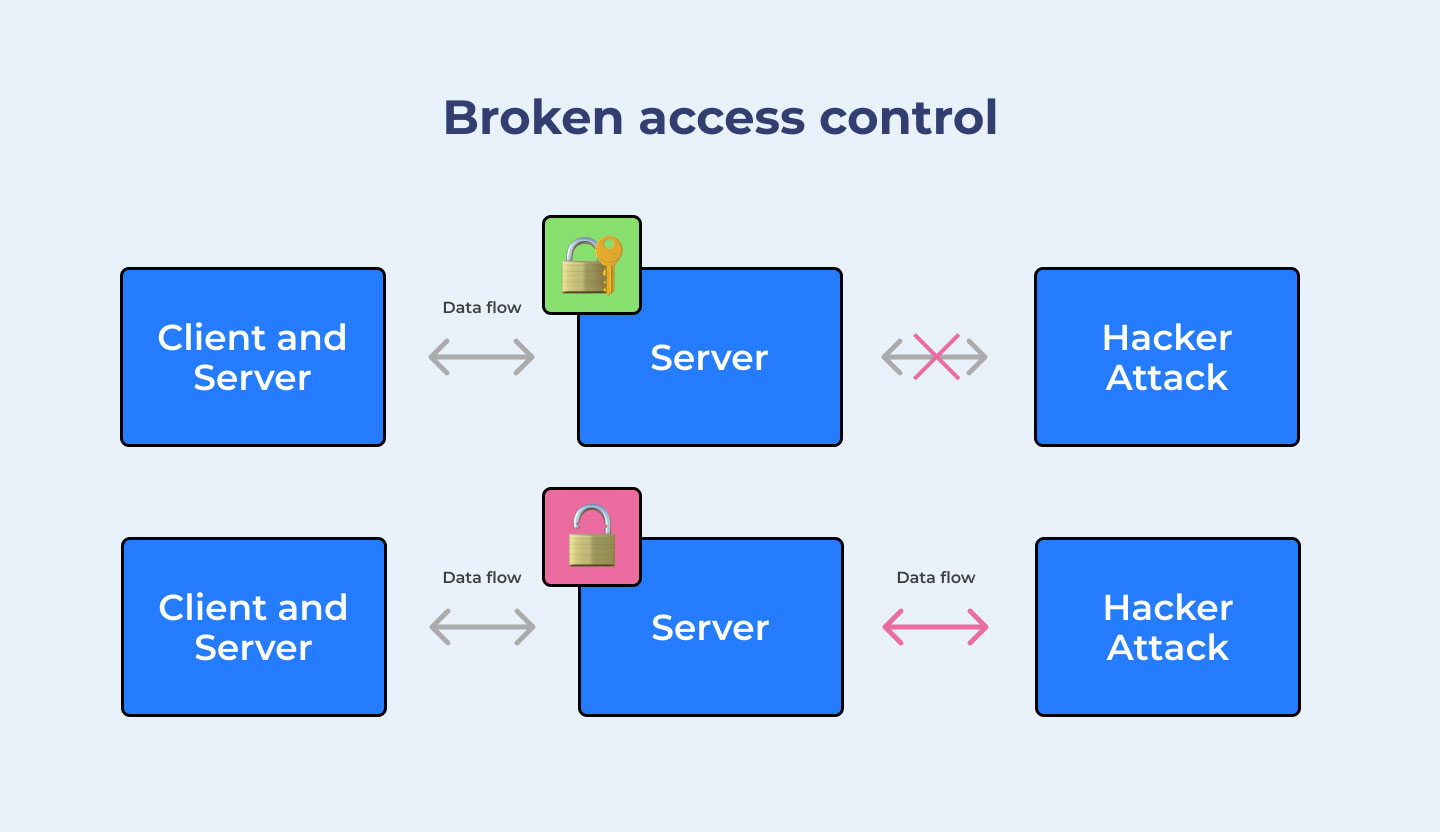
Access control is control over what users can and cannot do. When it’s not properly enforced, it means users can perform actions that can affect your website in unpredictable ways. One way to exploit broken access control is by viewing and editing other users’ profiles and data. Another is accessing premium features without paying for or earning them. Yet another is accessing admin pages from a non-admin account (or worse, without an account at all).
The best way to ensure your website’s access control is working is manual testing. No automated testing tools can guarantee that access control works as intended.
Broken access control can also result from abusing the cross-origin resource sharing (CORS) mechanism, which can provide access to otherwise restricted APIs. For this reason, it’s recommended to use CORS as little as possible.
Insecure deserialization
Serialization is the process of transforming an object into a binary code. Deserialization is, logically, the opposite. Both are processes conducted regularly in web development, which makes it important to implement protections against employing them in attacks.
The good news is that deserialization isn’t something a regular user or your employee can do accidentally. That’s also, in part, the bad news — deserialization attacks are always deliberate and, hence, vicious. They also result in the most serious issues, like running remote code, entering the website without authentication, and initiating DoS (denial of service) attacks.
The easiest way to secure your website from this type of attack is to forbid user-generated serialized objects. If this can’t be done, the next best option is to use cryptographic signatures for integrity checks.
Using JSON, YAML, or XML can make exploiting deserialization weaknesses harder for hackers since these formats aren’t binary.
Insufficient logging and monitoring

This vulnerability seems pretty obvious: if you don’t monitor your website and don’t log all errors and failed attempts to log in or execute access control functionality, you’re basically tempting hackers to attack your website. In any type of war, digital or real-life, the first attack usually isn’t about winning but about seeing what you’re up against. And if there’s an easy way in, you use it. Failure to log and monitor such probing will result in your system missing the attack altogether or detecting it once it’s already taken place and the damage is done.
Logging is particularly important for e-commerce sites, since they deal with users’ money and financial credentials.
To make a website secure from hackers, properly log all failed attempts and make sure these logs are stored and backed up outside your local servers. Employ automatic alerting systems for such failures, and, if possible, suspend accounts that continuously generate such failures. It’s vital to have real-time alerting systems so you can react to a possible breach immediately.
XML external entities (XXE)
We’ve mentioned XML (Extensible Markup Language) a couple of times already. It’s a flexible language, which makes it easy to use and widespread. XML processors parse data from XML documents. If your website is XML-based and accepts XML uploads without validation, it can be susceptible to attacks.
To protect your website’s integrity, the following set of actions is recommended:
- Disable DTD (document type definition) processing.
- Limit or prevent XML uploads, or, if that can’t be done, enforce whitelisting — positive server-side input validation.
- Regularly upgrade your XLM processors and libraries.
- Prevent serialization of sensitive data.
- Where applicable, use JSON or similar simple formats.
- Implement Web Application Firewalls (WAFs) and API security gateways.
Using components with known vulnerabilities
Nothing is perfect, and any component you use in your software is bound to have some vulnerability, known or unknown. In response to discovered and recognized vulnerabilities, software is updated to cover those vulnerabilities or mitigate any damage that may be caused by their exploitation. Some weaknesses cause minor damage, but others might be damning to your business.
To prevent website hacking due to known vulnerabilities, it’s important to regularly check for updates and update all components used on your website. This can be a tedious task in component-heavy software and websites. That’s why security experts recommend regularly checking for and removing unnecessary and unused libraries, features, files, and other components. And, of course, only use components from official sources. Don’t be seduced by websites that distribute usually paid software for free — it can be modified to hack your website.
14 Expert tips to protect your website from hackers

To put all the tech-heavy information in layman’s terms,here are security tips to protect a website from hackers or create a secure website:
- Find a reliable web host.
- Regularly update all software, frameworks, and libraries used on your website.
- Remove any unnecessary features and components from your website.
- Set up systems to validate input on both the browser and server sides.
- Monitor the information displayed in error messages.
- Set up a password strength checker for users.
- Always use strong passwords for your servers and admin pages, and change them regularly.
- Invest in an SSL certificate / use the HTTPS protocol.
- Set up proper logging for failures and errors.
- Log audit transactions (especially if yours is an e-commerce website).
- Monitor logs closely.
- Use cloud servers, but protect your data nonetheless.
- Always encrypt sensitive data using the latest technologies.
- Have your security team keep an eye on emerging security updates as well as new threats to be able to react to attacks in a timely fashion.
How much does it cost to secure a website?
This is a question to which there’s no definite answer. The cost of security depends heavily on the tech stack your site uses. Plus, there’s the cost of updates, which will depend on how many components you need to update, how often you update them, and how much updating each of them costs. These costs need to be calculated individually by your developers.
We strongly recommended taking security into consideration from the very beginning of development. Leaving the issue of security until the end might (and most probably will) result in a need to introduce changes to the core of your site, which can be even more expensive than building in security from the get-go.
Conclusion
If you’re a developer yourself, own a development company, or have an in-house development team, you can set all these tasks before them. However, if you don't already have technical specialists on your side and you want to know how to create a secure website with an outsourcing provider, we recommend finding a development company that can not only build a website but support it. It’s nearly impossible to predict every vulnerability, but the ability to react to any breach in a timely fashion can save your website from the worst of fates.
The developers at Mind Studios are experienced in the best security practices and keep up with the newest trends. If you have questions about how to secure your website from hackers, contact us for a free consultation.
Written by Svitlana Varaksina and Artem Chervichnik